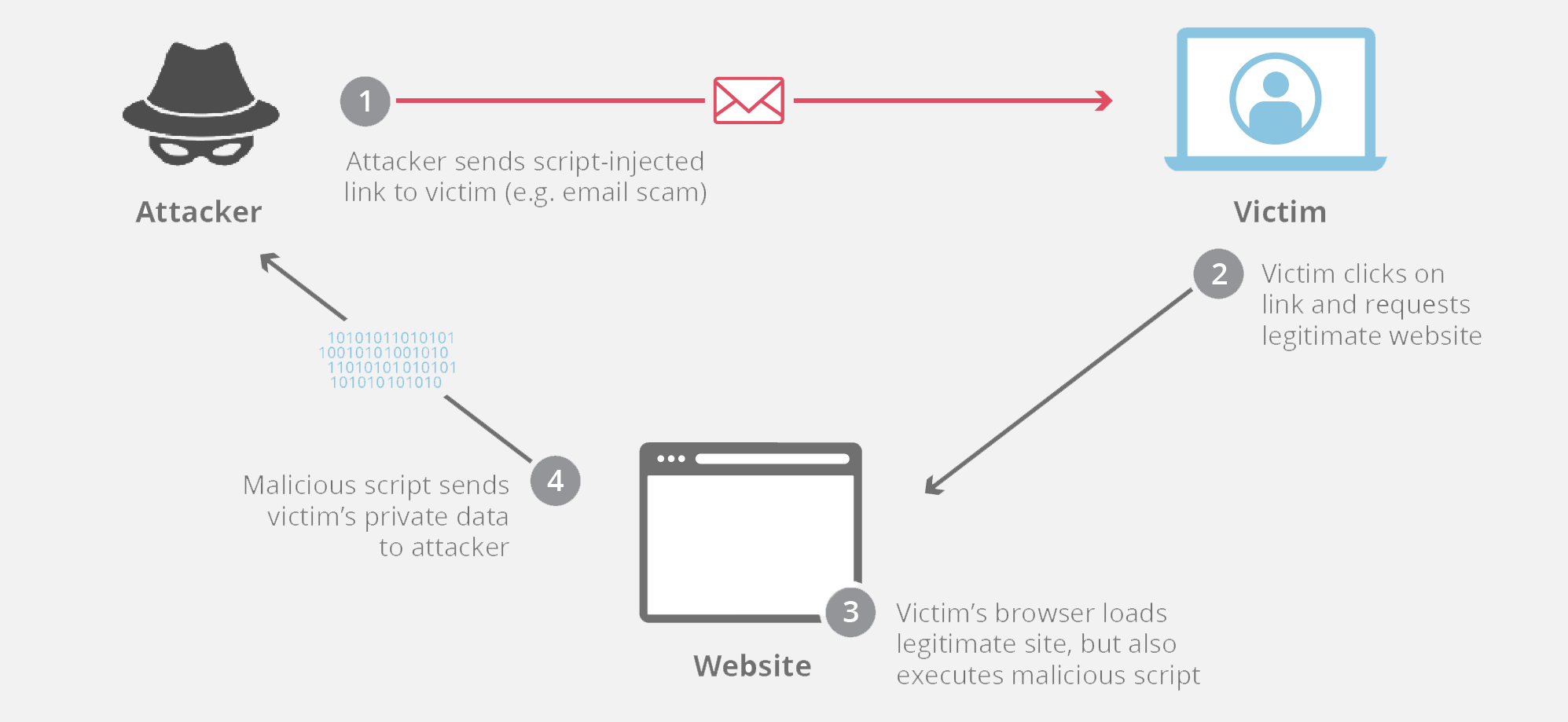
XSS Injection with SQLi (XSSQLi) XSS Injection with SQLi (XSSQLi) Well After our discussion on different types of injection and places you can find SQL injection Vulnerability, an attacker can successfully exploit and SQL injection vulnerability and get access over the database and if he is enough lucky to get access to the File System…
XSS Injection with SQLi
Posted on