Renzi Top VIP Security Researcher of the Month | Security Researcher Profile
Top VIP Security Researcher of the Month | Security Researcher Profile
Security researcher Renzi has already helped fix 7680 vulnerabilities.
Researcher reputation: 570
Real name:
Felipe Gabriel Renzi
About me:
-> Cyber Security Analyst and Security Researcher (Brazil).
-> We can make Web a Safer Place.
Note: Please, if you fixed vulnerability, don't forget to give me recommendations in my OBB Profile.
Contact email:
-> E-mail: [email protected]
-> Contact me as soon as possible to protect your web application!
Certifications & Diplomas:
-> Forest Engineering - UNESP
-> Information Security - SENAC
Experience in Application Security
over 5 years
Award / Bug Bounty I prefer:
-> Bounty Payment (PayPal).
-> Public Recognition & thanks (Here).
-> Swag (T-shirt, stickers, cups).
-> Vouchers (eg. Amazon Brazil)
Halls of Fame:
SoundCloud, Western Union, Alibaba, T-mobile, Telefonica, Tim, Huawei, Skyscanner, Jet, MasterCard, Wp Engine, Indeed, Costant Contact, Engel & Volkers Technology GmbH, U.S. Dept Of Defense, MTN and..
Ethics and Rules:
Felipe Gabriel Renzi is required to abide by the ethics and rules of the Open Bug Bounty project. If you reasonably believe that rules are not respected, please report this to us.
Recommendations and Acknowledgements
 2 February, 2021
2 February, 2021| Thanks Felipe for bringing this XSS vulnerability to our attention in a timely and professional manner. |
 2 May, 2019
2 May, 2019| Felipe found a XSS flaw in one of our web pages, and kindly told us about it so that we could address it. We'd like to thank Felipe for his prompt and professional disclosure. |
 30 April, 2019
30 April, 2019|
Felipe kindly pointed out an XSS problem to us. Thanks to his support, we were able to solve the problem quickly. Thank you very much Felipe, your help is highly appreciated! |
 25 April, 2019
25 April, 2019| Felipe fand einen XSS Fehler in einer unserer Web-Seiten und gab uns Tipps für ein sicheres Internet. Vielen Dank. |
 23 April, 2019
23 April, 2019| Felipe found a XSS security vulnerability in one of our customers site. We fixed it accordingly. He was very fast in answering and very supportive. Thank you very much, your help is highly appreciated! We will keep you in mind for future security checks on other websites. |
 15 April, 2019
15 April, 2019|
Felipe found a vulnerability in our website , which we were able to fix with Felipes detailed report. He was very responsive and professional. Highly recommended! Thank you very much Felipe! |
 22 January, 2019
22 January, 2019| Following Felipe's disclosure, we have now fixed the Reflected Cross-Site Scripting web vulnerability you discovered in our "www.majestic12.co.uk" web-application. We'd like to thank Felipe for his prompt and professional disclosure. |
 22 January, 2019
22 January, 2019| Found a xss issue, quickly emailed with the affected pages and links to aid resolving. Many thanks |
 2 November, 2018
2 November, 2018| Felipe found a XSS flaw in one of our researchers' web pages, and kindly told us about it so that we could address it. Thank you, Felipe. |
Shows the first 10 recommendations. See all.
Honor Badges
Number of Secured Websites
|
|
|
|
|
|
10+ Websites
|
50+ Websites
|
500+ Websites
|
WEB SECURITY VETERAN
1000+ Websites
|
Advanced Security Research
|
|
|
|
|
|
WAF Bypasser
|
CSRF Master
30+ Reports
|
AppSec Logic Master
30+ Reports
|
Fastest Fix
Fix in 24 hours
|
Outstanding Achievements
|
|
|
|
|
|
Secured OBB
|
OBB Advocate
|
Improved OBB
|
Commitment to Remediate and Patch
|
|
|
|
|
|
Patch Master
55% Patched
|
Patch Guru
65% Patched
|
Patch Lord
75% Patched
|
Recommendations and Recognition
|
|
|
|
|
|
REPUTABLE
10+ Recommends
|
FAMOUS
25+ Recommends
|
GLOBALLY TRUSTED
50+ Recommends
|
Distinguished Blog Author
|
|
|
|
|
|
1 Post
|
3 Posts
|
5+ Posts
|
Research Statistics
| Total reports: | 16414 |
| Total reports on VIP sites: | 49 |
| Total patched vulnerabilities: | 7680 |
| Recommendations received: | 37 |
| Active since: | 31.05.2018 |
| Top Security Researcher Awards: |  Top Security Researcher of the Month
Top Security Researcher of the Month |
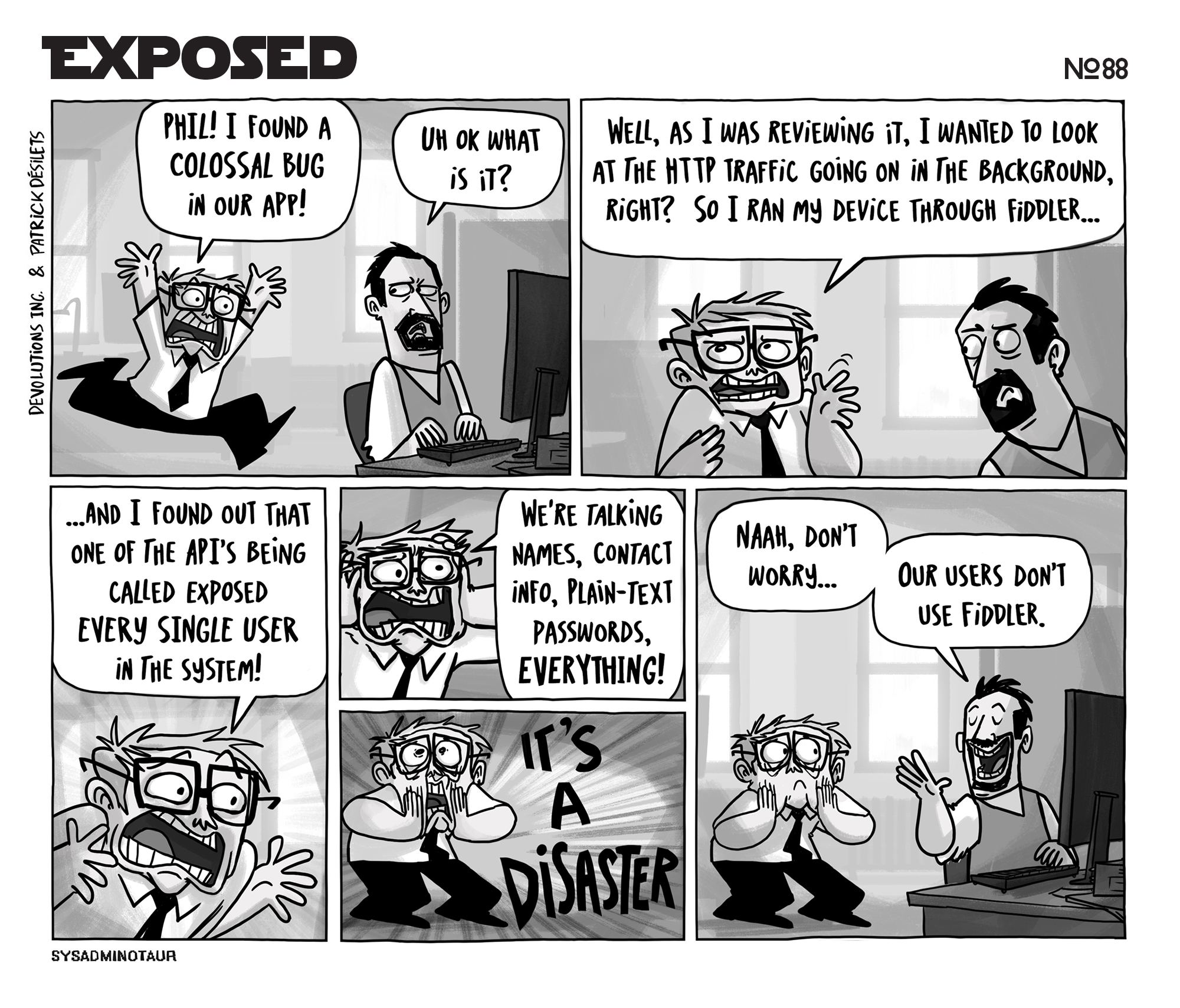
10.02.2021 Sysadminotaur nº88
01.10.2019 #Security 100%

13.08.2019 XSSCon - XSS Tool @Kitploit
Powerfull Simple XSSScanner made with python 3.7

Download: https://github.com/menkrep1337/XSSCon
Reference: https://www.kitploit.com
01.05.2019 1000's of default passwords on http://open-sez.me

01.05.2019 Fuxploider - @almandin

" Fuxploider is an open source penetration testing tool that automates the process of detecting and exploiting file upload forms flaws. This tool is able to detect the file types allowed to be uploaded and is able to detect which technique will work best to upload web shells or any malicious file on the desired web server. "

 Platform update: please use our
Platform update: please use our 

 24 September, 2019
24 September, 2019 26.04.2024
26.04.2024 



Please login via Twitter to add a recommendation