macrogids.be Cross Site Scripting Vulnerability
Report ID: OBB-1532242
Security Researcher devl00p
Helped patch 92748 vulnerabilities
Received 11 Coordinated Disclosure badges
Received 37 recommendations
, a holder of 11 badges for responsible and coordinated disclosure, found Cross Site Scripting security vulnerability affecting macrogids.be website and its users.
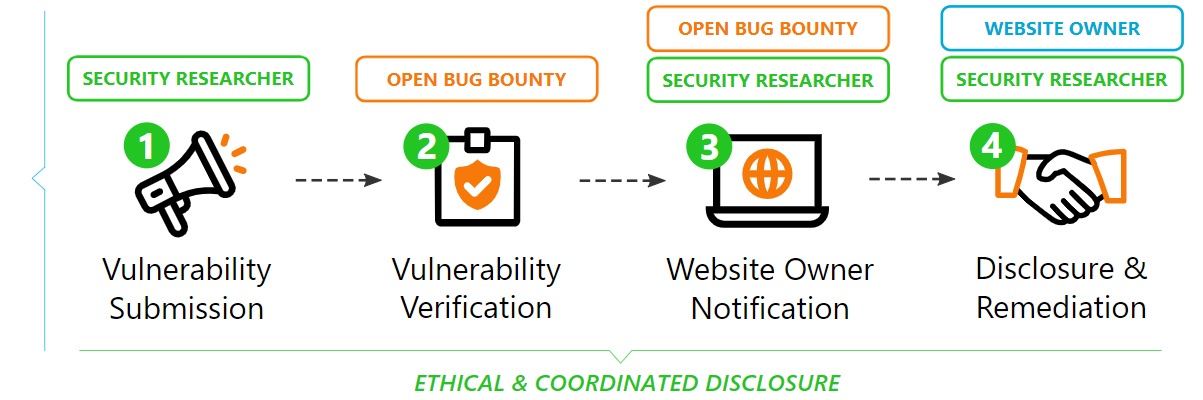
Following the coordinated and responsible vulnerability disclosure guidelines of the ISO 29147 standard, Open Bug Bounty has:
a. verified the vulnerability and confirmed its existence;
b. notified the website operator about its existence.
| Affected Website: | macrogids.be |
| Open Bug Bounty Program: | Create your bounty program now. It's open and free. |
| Vulnerable Application: | Custom Code |
| Vulnerability Type: | XSS (Cross Site Scripting) / CWE-79 |
| CVSSv3 Score: | 6.1 [CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N] |
| Disclosure Standard: | Coordinated Disclosure based on ISO 29147 guidelines |
| Discovered and Reported by: | devl00p
Helped patch 92748 vulnerabilities Received 11 Coordinated Disclosure badges Received 37 recommendations |
| Remediation Guide: | OWASP XSS Prevention Cheat Sheet |
| Export Vulnerability Data: | Bugzilla Vulnerability Data JIRA Vulnerability Data [ Configuration ] Mantis Vulnerability Data Splunk Vulnerability Data XML Vulnerability Data [ XSD ] |
Vulnerable URL:
HTTP POST data:
Research's Comment:
Mirror: Click here to view the mirror
Coordinated Disclosure Timeline
| Vulnerability Reported: | 21 November, 2020 11:58 GMT |
| Vulnerability Verified: | 21 November, 2020 12:14 GMT |
| Website Operator Notified: | 21 November, 2020 12:14 GMT |
| a. Using the ISO 29147 guidelines |  |
| b. Using publicly available security contacts |  |
| c. Using Open Bug Bounty notification framework |  |
| d. Using security contacts provided by the researcher |  |
| Public Report Published [without technical details]: | 21 November, 2020 12:14 GMT |
| Public Disclosure: | 19 February, 2021 11:58 GMT |
For Website Operators and Owners
Please read how Open Bug Bounty helps make your websites secure and then contact the researcher directly to get the vulnerability details. The researcher may also help you fix the vulnerability and advice on how to prevent similar issues:
For remediation best practices, please also refer to OWASP remediation guidelines. More information about coordinate and responsible disclosure on Open Bug Bounty is available here.
DISCLAIMER: Open Bug Bounty is a non-profit project, we never act as an intermediary between website owners and security researchers. We have no relationship or control over the researchers. Our role is limited to independent verification of the submitted reports and proper notification of website owners by all reasonably available means.
macrogids.be
Website Overview and Rating
| SSL/TLS Server Test: | B+ View Results |
| Web Server Security Test: | C View Results |
| Malware Test: | Click here |
| Domain Health Report: | Click here |
Latest Submissions
| OBB-ID | Reported by | Status | Reported on |
|
patched
|
27.11.2020
|
||
|
unpatched
|
24.11.2020
|
||
|
unpatched
|
21.11.2020
|
||
|
unpatched
|
17.11.2020
|
||
|
patched
|
14.11.2020
|
||
|
unpatched
|
11.11.2020
|
||
|
unpatched
|
08.11.2020
|

 Platform update: please use our
Platform update: please use our 





